AI in Cybersecurity: Threat Detection and Response
How artificial intelligence is transforming cybersecurity from reactive defense to proactive threat hunting, enabling organizations to detect and respond to threats faster than ever before.

The cybersecurity landscape has never been more challenging. Attack vectors are multiplying, threat actors are becoming more sophisticated, and the attack surface is expanding as organizations embrace digital transformation. Traditional security approaches—signature-based detection, rule-based response—cannot keep pace with this evolving threat landscape. Artificial intelligence offers a new approach: systems that can learn from data, detect anomalies that humans would miss, and respond to threats at machine speed. This article examines how AI is transforming cybersecurity, from threat detection and vulnerability management to incident response and security operations.
Introduction
Cybersecurity is fundamentally a data problem. Organizations generate enormous amounts of security-relevant data: network logs, authentication events, system calls, email headers, file access patterns. Human analysts cannot possibly review all this data to identify threats. The result is that many attacks go undetected for months—the average time to detect a breach is over 200 days.
Artificial intelligence offers a solution to this data overload. Machine learning models can analyze security data at scale, identifying patterns and anomalies that indicate compromise. They can learn from historical attacks to detect new variants. They can automate response to common threats, freeing human analysts to focus on complex cases.
This transformation is not incremental—it is foundational. AI-powered security represents a fundamentally different approach to threat management, one that can keep pace with evolving threats rather than constantly falling behind.
The Threat Landscape
Understanding what AI must detect requires understanding the threats it must detect. The modern threat landscape is diverse, sophisticated, and constantly evolving.
Malware remains a primary threat vector. Malicious software takes many forms: viruses that replicate across systems, ransomware that encrypts files for payment, trojans that create backdoors for future access, spyware that exfiltrates sensitive data. Attackers continuously develop new variants designed to evade traditional detection.
Phishing targets humans rather than systems. Attackers send emails that appear legitimate—requests from "IT" to reset passwords, invoices from "vendors," shipping notifications from "carriers." These attacks succeed because they exploit human trust rather than software vulnerabilities.
Insider Threats come from within organizations. Disgruntled employees, compromised contractors, and malicious insiders have access that external attackers cannot easily obtain. These threats are particularly difficult to detect because their authorized access makes malicious activity appear legitimate.
Supply Chain Attacks target the software ecosystem. By compromising software vendors, attackers can gain access to all of a vendor's customers simultaneously—as demonstrated by attacks like SolarWinds and Log4j. These attacks are particularly challenging because they exploit trust relationships.
Zero-Day Exploits target unknown vulnerabilities. Because these vulnerabilities are unknown to defenders, traditional detection based on known signatures cannot detect them. Attackers who discover zero days can penetrate even well-defended networks.
Ransomware has become particularly lucrative for attackers. By encrypting organizational data and demanding payment, attackers can extort enormous sums. The rise of "ransomware-as-a-service" makes these attacks accessible to less sophisticated attackers.
AI Approaches to Threat Detection
AI-powered threat detection uses multiple approaches, each suited to different detection challenges.
Anomaly Detection identifies activity that deviates from normal. Machine learning models learn what "normal" looks like—normal login times, normal data access patterns, normal network traffic—and flag deviations for investigation. This approach can detect novel attacks that would evade signature-based detection.
The challenge is defining "normal." Activity that is unusual but not malicious (a user working late on a project) should not trigger alerts, while subtle attacks (slow data exfiltration over months) may not appear anomalous enough. Modern approaches use context—time, role, project—to distinguish legitimate unusual activity from genuine threats.
Signature-Based Detection using AI improves on traditional signature matching. Rather than exact signatures, AI models learn approximate patterns that match attack variants. This approach can detect new variants of known attacks while maintaining the efficiency of signature-based detection.
Behavioral Analysis examines how entities (users, devices, applications) behave over time. An account that suddenly accesses unusual data or a device that communicates with unusual network addresses might be compromised. Behavioral analysis can detect slow, persistent attacks that evaded initial detection.
Threat Intelligence leverages external data about known threats. AI models can correlate internal activity with external threat intelligence, prioritizing alerts that match known attack patterns with higher confidence.
Vulnerability Management
AI is also transforming how organizations identify and manage vulnerabilities.
Automated Vulnerability Discovery uses AI to identify security weaknesses in code and configurations. These tools can scan codebases continuously, identifying vulnerabilities before they reach production. The result is more secure software with less security expertise.
Prioritization uses AI to rank vulnerabilities by likely exploitability. Not all vulnerabilities are equally likely to be exploited—some require specific conditions, others have limited exposure. AI models can predict which vulnerabilities attackers are most likely to target, enabling efficient remediation.
Penetration Testing uses AI to simulate attacks. AI-powered tools can automatically probe systems, identify weaknesses, and attempt exploitation—providing continuous penetration testing rather than periodic assessments.
Security Operations Centers
AI is transforming how security operations centers (SOCs) function.
Alert Triage uses AI to prioritize security alerts. Rather than treating all alerts equally, AI models can assess the likely severity and relevance of alerts, enabling analysts to investigate the most critical issues first.
Investigation Assistance provides AI tools that assist human investigators. These tools can correlate data across sources, suggest next steps, and retrieve relevant information. The result is faster, more thorough investigations.
Automated Response can contain threats without human intervention. When AI models detect high-confidence threats—isolating compromised devices, blocking network traffic, resetting credentials—they can respond immediately, before humans even become aware of the threat.
Market Overview
The AI cybersecurity market is experiencing rapid growth, driven by increasing threat sophistication and security talent shortages.
| Company | Primary Focus | Notable Products |
|---|---|---|
| CrowdStrike | Endpoint security | Falcon platform |
| Palo Alto Networks | Firewall/Security | Cortex platform |
| SentinelOne | Endpoint protection | Singularity platform |
| Darktrace | Anomaly detection | Enterprise Immune System |
| IBM | Security operations | QRadar |
Challenges and Limitations
Despite progress, AI-powered security faces significant challenges.
False Positives remain a fundamental problem. Alert fatigue—ignoring alerts because too many are false—defeats the purpose of detection. AI models must balance detection sensitivity with specificity.
Adversarial Attacks target AI systems themselves. Attackers can craft inputs designed to evade AI detection—malware that looks benign, phishing that evades classifiers. This creates an ongoing adversarial dynamic.
Data Requirements for training effective models are substantial. Organizations need labeled data—examples of attacks and non-attacks—for training. This data is often scarce, particularly for novel attack types.
Explainability is essential for security acceptance. Analysts need to understand why an alert was triggered to effectively investigate. Complex AI models can be "black boxes" that provide limited explanation.
The Future
AI in cybersecurity will continue to evolve toward more autonomous systems.
Proactive Threat Hunting will become standard. Rather than waiting for alerts, AI systems will actively search for threats—identifying indicators of compromise that passive detection would miss.
Zero-Trust Architecture extends AI across security domains. AI will assess trust continuously, not just at login—evaluating each access request in context.
Secure-by-Design integrates AI into development. AI will identify vulnerabilities during development, not after deployment, shifting security left in the development process.
Conclusion
AI is transforming cybersecurity from reactive defense to proactive threat management. The ability to detect anomalies, learn from data, and respond at machine speed addresses fundamental limitations of traditional approaches.
The challenges—false positives, adversarial attacks, data requirements—are significant but tractable. The trajectory is clear: AI-powered security will become standard, and organizations that do not adopt these technologies will face increasing risk.
For security professionals, AI represents a powerful tool for augmenting human capabilities, not replacing them. For organizations, AI represents an essential capability for managing cyber risk. The future of cybersecurity is artificial.
Related Articles

Adobe Firefly 2026: The Generative AI Revolution in Creative Cloud
How Adobe's Firefly integrates with Creative Cloud to transform creative workflows with unlimited generative AI
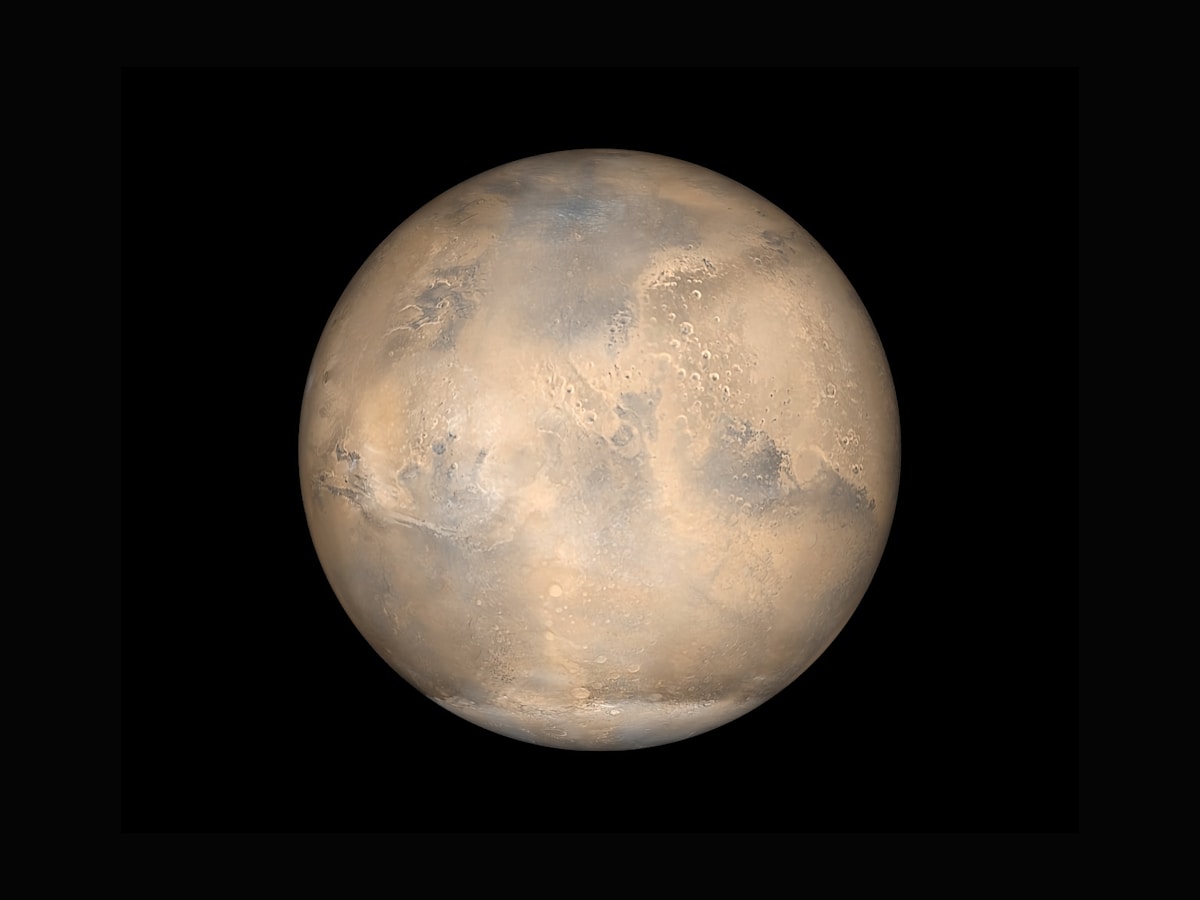
NASA Perseverance AI-Driven Mars Mission: The First Autonomous Interplanetary Drive
How NASA's Perseverance rover completed the first AI-planned drive on Mars using Anthropic's Claude vision-language models

OpenAI Sora Shutdown: The Rise and Fall of AI Video's Flagship Product
An in-depth analysis of OpenAI's decision to shut down Sora, the collapse of the $1 billion Disney deal, and what this means for the future of AI-generated video.
