NemoClaw: NVIDIA's Answer to OpenClaw's Security Gap
How NVIDIA built a kernel-level security layer for autonomous agents—and why it matters for production AI deployments in regulated industries.
If you ask anyone deep in the OpenClaw ecosystem a simple question: "How do you isolate tenant data?" or "What policy actually governs outbound network access?"—the conversation tends to get vague really fast.
Until very recently, the honest answer was usually some version of "We're trying to be careful."
The same architecture that made OpenClaw exciting also made it difficult to trust in production. Security incidents piled up, and questions around agent identity, outbound access, secrets handling, and deployment boundaries became critical for serious production workloads. Nobody wants a heavy operational liability.
That's why Meta banned it from corporate machines and LangChain distanced itself.
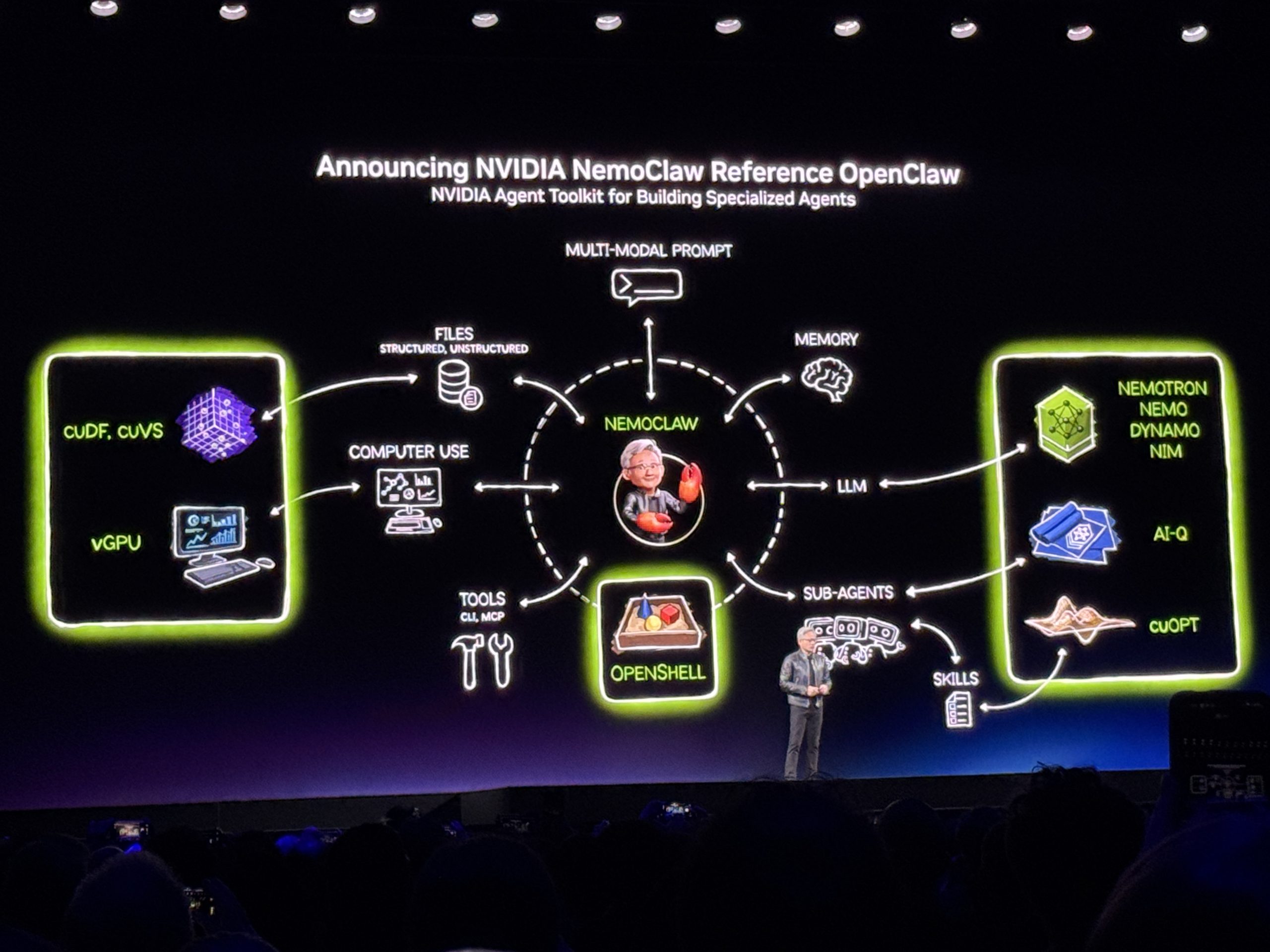
That is the gap NVIDIA stepped into at GTC 2026 with NemoClaw—addressing the infrastructure-level security gap for autonomous agents in an architecturally sound way.
What Is NemoClaw?
Think of it this way: OpenClaw is the assistant, and NemoClaw is NVIDIA's controlled runtime and security layer around it.
NemoClaw is essentially an "OpenClaw plugin for NVIDIA OpenShell." It's a thin TypeScript package that registers commands under openclaw nemoclaw, runs in-process with the OpenClaw gateway, and handles user-facing CLI interactions.
This distinction changes how you should evaluate the project entirely:
- If you want the assistant experience itself, you're still evaluating OpenClaw.
- If you want stricter runtime controls around that assistant—sandboxing, policy enforcement, inference routing, deployment governance—you're evaluating NemoClaw plus OpenShell.
It's the infrastructure that makes the application safe to run in production.
The Architecture in Three Layers
NemoClaw's architecture breaks down into three distinct layers, each solving a different class of problem:
Layer 1: OpenShell (The Sandbox Runtime)
OpenShell is NVIDIA's open-source secure runtime for autonomous agents. Every agent runs inside a hardened sandbox built on:
- Landlock: Linux security module for filesystem access control
- seccomp: System call filtering that blocks privilege escalation and dangerous syscalls at the kernel level
- Network namespaces: Full network isolation per agent—not shared Docker networking, but real namespace-level isolation
- Process isolation: Even if a compromised dependency tries to escalate privileges or execute kernel-level operations, the sandbox prevents it
I've seen too many sandboxed agent platforms that are just Docker containers with
--privilegedquietly enabled.
OpenShell takes a fundamentally different approach.
Layer 2: NemoClaw (The Policy and Deployment Bridge)
NemoClaw connects OpenClaw to OpenShell and adds the policy-aware controls around how the assistant runs.
It introduces blueprints—versioned configuration files that orchestrate:
- Sandbox creation parameters
- Security policy definitions
- Inference provider routing
- Session monitoring rules
- Operator approval workflows
One command spins up a fully isolated agent environment:
curl -fsSL https://nvidia.com/nemoclaw.sh | bash
nemoclaw onboard
The onboard command walks you through connecting your inference provider, setting filesystem policies, and configuring network access rules.
Layer 3: Inference Routing
The inference layer supports three distinct profiles:
- NVIDIA-hosted inference: Cloud API calls to NVIDIA's managed endpoints
- Local NIM (NVIDIA Inference Microservice): Running models like Nemotron locally on NVIDIA hardware
- Self-hosted vLLM: Running open models on your own infrastructure
All three are governed by the same policy layer, the same security controls, and the same audit trail.
This solves the problem I've heard from every healthcare, finance, and legal prospect: "We cannot send our data to an external API. Full stop."
For anyone who's ever tried to sell AI agent services to a regulated industry, you know how transformative this is. The conversation goes from "We'll figure out data residency later" to "Here's the policy file, audit it yourself."
Quick Start with NemoClaw
Setup is fairly straightforward with standard prerequisites.
Prerequisites
Before you touch NemoClaw, make sure you have:
- Linux: Ubuntu 22.04 or newer. The Landlock and seccomp integrations are Linux-specific. If you're on macOS, you'll need a VM or remote server.
- Docker: Required for container-based components.
- GitHub CLI: The OpenShell binary is distributed via GitHub releases, and you need
ghauthenticated. - NVIDIA GPU (recommended but not required): NemoClaw is hardware-agnostic, but local NIM inference obviously requires NVIDIA hardware.
Step 1: Install the NemoClaw CLI
curl -fsSL https://nvidia.com/nemoclaw.sh | bash
The nemoclaw CLI is the primary entrypoint for setting up and managing sandboxed OpenClaw agents. It delegates heavy lifting to a versioned blueprint—a Python artifact that orchestrates sandbox creation, policy application, and inference provider setup through the OpenShell CLI.
When the install completes, a summary confirms the running environment:
──────────────────────────────────────────────────
Sandbox my-assistant (Landlock + seccomp + netns)
Model nvidia/nemotron-3-super-120b-a12b (NVIDIA Cloud API)
──────────────────────────────────────────────────
Run: nemoclaw my-assistant connect
Status: nemoclaw my-assistant status
Logs: nemoclaw my-assistant logs --follow
──────────────────────────────────────────────────
[INFO] === Installation complete ===
You can then connect to the sandbox and chat with the agent through the TUI or the CLI:
nemoclaw my-assistant connect
That's it.
NemoClaw vs. OpenClaw
| Feature | OpenClaw | NemoClaw |
|---|---|---|
| Assistant experience | ✅ Native | Via plugin |
| Sandbox isolation | ❌ None | ✅ Landlock + seccomp + netns |
| Policy enforcement | ❌ None | ✅ Blueprint-based |
| Local inference | ❌ External only | ✅ NIM + vLLM |
| Network isolation | ❌ Shared | ✅ Per-agent namespaces |
| Audit logging | Basic | Full session monitoring |
NemoClaw is a great option that combines open-source transparency with kernel-level security and local inference support.
What NemoClaw Doesn't Solve (Yet)
No tool solves everything, and being honest about limitations is how you build trust.
Observability Is Still Nascent
NemoClaw provides session monitoring and basic activity logs, but it's not yet at the level of observability you'd expect from production infrastructure. There's no built-in integration with Datadog, Grafana, or OpenTelemetry. You'll need to build your own monitoring pipeline on top of what NemoClaw provides.
No GUI for Non-Technical Operators
Everything in NemoClaw is CLI-driven. That's fine for developers, but if your product team needs to manage agent deployments, they'll need training or a custom dashboard. The onboarding flow is interactive and reasonably friendly, but day-to-day operations require comfort with the terminal.
Testing Frameworks Don't Exist Yet
There's no built-in way to test agent behavior inside a sandbox before deploying to production. No dry-run mode for policy changes. No simulation environment for validating that a policy file actually permits the agent's required workflows.
Multi-Cloud Orchestration Is Out of Scope
NemoClaw deploys agents on a single host or cluster. If you need agents running across AWS, GCP, and on-premises simultaneously—with consistent policy enforcement—NemoClaw doesn't handle cross-environment orchestration. You'll need a federation or your own control plane on top.
Documentation Is Still Catching Up
The docs are good for alpha software but not comprehensive. I found myself reading the source code more often than I'd like. The distinction between plugin-side commands and host-side commands isn't always clear. Some features are documented in the GitHub README but not on the official docs site, and vice versa.
This is expected for alpha software—just go in with that expectation.
Concluding Thoughts
I want to end with the questions that are actually keeping me up at night:
- How will the policy model evolve for multi-agent systems?
- What happens when agents need to evolve their own policies?
NemoClaw represents a significant step forward in making autonomous agents safe for production use. The combination of kernel-level sandboxing, policy-as-code, and local inference support addresses the core concerns that have held back enterprise adoption of agent frameworks.
It's not perfect—no alpha software is. But it's the most promising direction I've seen for securing autonomous agents in regulated industries.
If you're building with NemoClaw or thinking about it, I'd love to hear about your experience.
Related Articles

AI Agent Security, Performance & Enterprise Deployment: The Deep Dive
we explored the fundamental philosophies behind OpenClaw, Manus AI, and Claude Code. Now it's time for the uncomfortable conversations — the ones every CTO and security lead needs to have before production deployment.

AI Agents: The Autonomous Future of Artificial Intelligence
Exploring AI agents—autonomous systems that can plan, execute, and adapt—revolutionizing how we interact with artificial intelligence.
Enterprise Integrations & Scaling: OpenClaw at Scale
Enterprise-grade OpenClaw integration guide covering Notion, GitHub, Google Workspace, Microsoft Teams, and more. Learn OAuth setup, authentication patterns, multi-team architectures, and scaling strategies for production deployments.